The SolarWinds hack exposed on Dec. 13 was used to access data from some 18,000 clients, making it one of the biggest cybersecurity breaches in history.
Malicious code hidden in one of the Austin, Texas-based tech company’s software products, Orion, resulted in data breaches for private companies, hospitals and government agencies alike. The attack is believed to have been sponsored by the Russian government.
While the hack isn’t considered an act of war, it’s time to reconsider the government’s cybersecurity strategy and how coordination will happen among businesses and government agencies.
Since this hack accessed hospitals and government agencies, vulnerabilities in the system could allow larger-scale cyber attacks to occur, possibly affecting COVID-19 vaccine availability or U.S. military logistics.
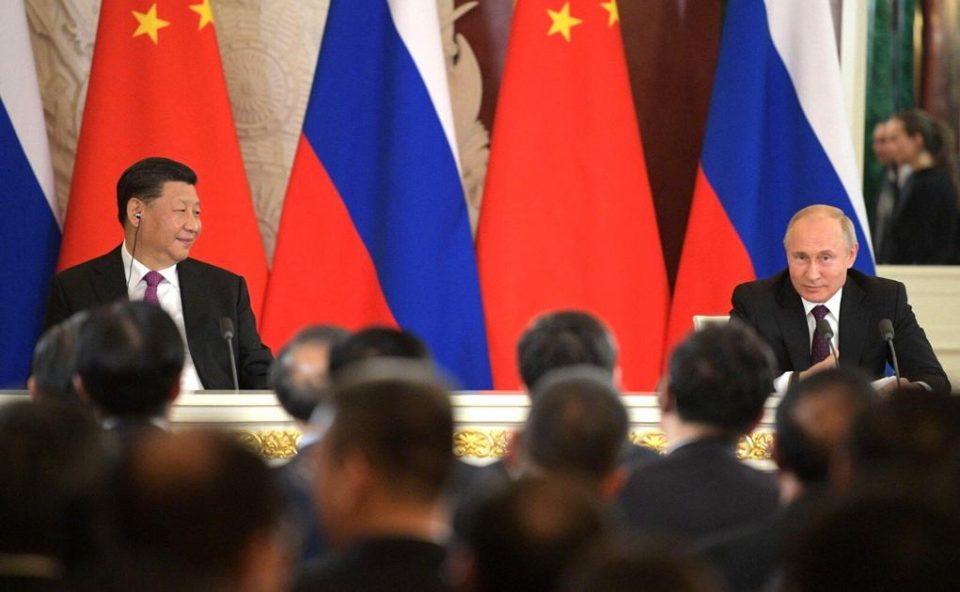
Security threats rise along with China, Russia. Is the U.S. ready?
The need to shore up cyber defenses and increase the costs of attacking U.S. cyberspace has been a long time coming. China and Russia have spent decades developing modern warfare technologies that render America’s massive logistics system vulnerable. Those two global powers likely have the technology to attack the U.S. logistics network or U.S. weapons systems, or the private businesses like SolarWinds that sell products to these agencies.
The attack on SolarWinds came despite U.S. government attempts to strengthen cybersecurity. There’s a consensus among actors in the government and the private sector that the U.S. needs a coordinated cybersecurity strategy that’ll hold adversaries accountable for attacks like this one to prevent more damage in the future.
The Cyberspace Solarium Commission, a panel of government and non-government experts, issued a list of recommendations for U.S. strategy in March 2020. Many of these recommendations were incorporated into the National Defense Authorization bill, which is currently taking a circuitous trip around Capitol Hill.
Since the government is set up in a way that intra-agency sharing doesn’t really happen, responses to cyber attacks are “slow” and “laden with friction,” Sen. Angus King (I-ME) and co-chair of the Cyberspace Solarium Commission wrote. “The United States lacks the credibility we need to deter our enemies in cyberspace below the level of armed conflict,” King said.
King suggests the best move forward is a layered approach to national cyber defense strategy, deterring unwanted behavior by “blending elements of imposing costs with denial of benefits.”
In the past, the U.S. has relied on a strategy called “defend forward,” defined by the Department of Defense as “disrupt[ing] or halt[ing] malicious cyber activity at its source, including activity that falls below the level of armed conflict.” However, “defend forward” has been held back from responding swiftly to cyber attacks because of a lack of coordination on the part of the U.S.
“There’s no one place in the U.S. government where all the foreign intelligence gets merged with the domestic cyber hints and turned into action,” Glenn Gerstell, former NSA general counsel said, according to The Washington Post.
The strategy of “defend forward” can only be carried out with stronger coordination among the government and tech businesses. Because many government agencies use software products that come from tech companies like SolarWinds, an attack on any aspect of the supply chain can result in a breach for a government agency.
Brad Smith, president and chief legal officer of Microsoft, one of the companies impacted by the hack, wrote that this moment “requires that we look with clear eyes at the growing threats we face and commit to more collaborative and effective leadership.”
The SolarWinds attack should be a “moment of reckoning,” as Smith puts it, requiring that we “commit to more effective and collaborative leadership by the government and the tech sector in the United States, to spearhead a strong and coordinated global cybersecurity response.”
Jillian Lynch is a senior international affairs major. Contact Jillian at [email protected].
Disclaimer: I have no positions in any stocks mentioned and no plans to initiate any positions within the next 72 hours. I wrote this article myself and it expresses my own opinions. I’m not receiving compensation for it and I have no business relationship with any company whose stock is mentioned in this article.